I often notice confusion around NSA Suite B encryption because it sounds secretive and complex, yet its purpose was actually clarity and standardization. When I first studied it closely, I realized it was designed to simplify how strong cryptography could be shared across governments, industries, and global partners. Instead of hiding algorithms behind classified walls, Suite B openly defined which encryption, hashing, and key exchange methods were trusted for protecting sensitive but unclassified information. This article explores NSA Suite B encryption in a detailed, practical, and educational way so readers can clearly understand what it was, how it worked, why it mattered, and what replaced it. The focus here is not marketing or speculation but real technical and historical understanding written in a clear human tone.
What Is NSA Suite B Encryption
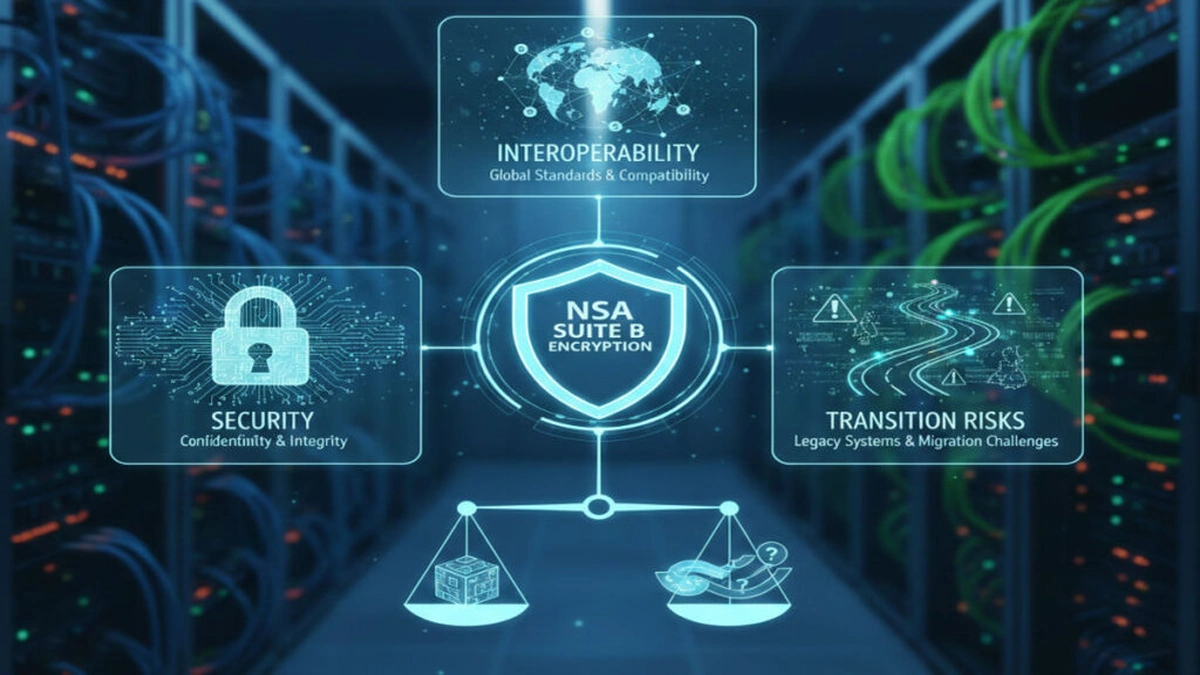
NSA Suite B encryption was a cryptographic framework published by the National Security Agency to define a set of publicly available algorithms approved for protecting classified and sensitive information. It was introduced to replace older, fragmented standards with a consistent and interoperable set of modern cryptographic tools.
Suite B did not invent new algorithms. Instead, it selected well studied, peer reviewed, and widely implemented cryptographic primitives. This approach allowed government agencies, defense contractors, and international allies to rely on the same encryption foundations without using classified algorithms.
Key Purpose of Suite B
The primary goal of Suite B was interoperability with strong security. Agencies and partners needed encryption that could work across different hardware, software, and national boundaries while still meeting strict security requirements.
Historical Background and Motivation
Before Suite B, cryptographic standards varied widely. Some systems used outdated algorithms, while others relied on classified methods that could not be shared with allies or commercial vendors. This created inefficiency, compatibility issues, and security risks.
NSA introduced Suite B in the mid 2000s to address these problems. By choosing algorithms already standardized by international bodies, NSA ensured transparency and long term trust.
Why Public Algorithms Were Chosen
Public algorithms allowed independent researchers to analyze and test their security. This openness reduced the risk of hidden weaknesses and increased confidence in their long term reliability.
Core Algorithms Used in NSA Suite B
NSA Suite B encryption relied on four main cryptographic components. Each served a specific security function.
Advanced Encryption Standard for Data Protection
AES was selected for symmetric encryption. It encrypts data using a shared secret key and is known for both strong security and high performance.
Suite B approved AES with 128 bit and 256 bit keys. The choice allowed flexibility between performance and higher security margins.
Elliptic Curve Cryptography for Key Exchange
Elliptic Curve Diffie Hellman and Elliptic Curve Digital Signature Algorithm were used for secure key exchange and authentication.
Elliptic curve cryptography provided strong security with smaller key sizes compared to traditional RSA, making it ideal for constrained environments.
Secure Hash Algorithm for Integrity
SHA 256 and SHA 384 were selected for hashing. These algorithms ensure data integrity and support digital signatures.
Hashes help verify that data has not been altered during transmission or storage.
Security Levels Defined by Suite B
Suite B defined two main security levels aligned with the sensitivity of information.
128 Bit Security Level
This level used AES 128, SHA 256, and elliptic curves offering comparable strength. It was suitable for protecting secret level information.
192 Bit Security Level
This higher level used AES 256, SHA 384, and stronger elliptic curves. It was intended for top secret level protection.
The clear separation helped organizations choose appropriate security without over engineering.
How NSA Suite B Was Implemented
Suite B was not a product or software package. It was a specification. Vendors implemented it in hardware devices, operating systems, secure communication tools, and cryptographic libraries.
Common Implementation Areas
Secure military communications, government VPNs, smart cards, and encrypted storage systems commonly adopted Suite B standards.
This widespread adoption improved interoperability across systems and organizations.
Advantages of NSA Suite B Encryption
Suite B offered several important benefits that contributed to its adoption.
Transparency and Trust
Because all algorithms were public, independent experts could evaluate their security. This reduced suspicion and increased global acceptance.
Efficiency and Performance
Elliptic curve cryptography reduced computational overhead while maintaining strong security. This made Suite B suitable for mobile and embedded systems.
Interoperability
Using standardized algorithms ensured compatibility between different vendors and countries.
Limitations and Criticism
Despite its strengths, Suite B was not without criticism.
Limited Algorithm Diversity
Suite B focused on a narrow set of algorithms. If a weakness were discovered, alternatives were limited within the framework.
Transition Challenges
Organizations using older cryptographic systems faced cost and complexity when migrating to Suite B compliant solutions.
Post Quantum Concerns
Suite B was designed before quantum computing became a major concern. Elliptic curve and RSA based systems may be vulnerable to future quantum attacks.
Relationship Between Suite B and Commercial Standards
Suite B closely aligned with standards from NIST and ISO. This alignment allowed commercial products to meet government requirements without custom cryptography.
Many widely used security protocols such as TLS adopted algorithms consistent with Suite B.
The Transition Away From NSA Suite B
In 2018, NSA officially transitioned from Suite B to the Commercial National Security Algorithm Suite. This shift reflected evolving security needs and emerging threats.
Why Suite B Was Retired
The retirement did not mean Suite B was insecure. Instead, it allowed NSA to introduce quantum resistant research paths and updated guidance without confusion.
Legacy Systems Still Using Suite B
Many systems continue to rely on Suite B algorithms today. AES, SHA 2, and elliptic curve cryptography remain trusted and widely used.
Suite B and Modern Cryptography
Although no longer actively promoted as a suite, the principles of Suite B still influence modern security design.
Emphasis on Open Standards
Modern cryptography continues to favor open, peer reviewed algorithms.
Layered Security Design
Suite B highlighted the importance of combining encryption, hashing, and authentication rather than relying on a single mechanism.
Practical Use Cases and Examples
Suite B algorithms are still present in everyday technology.
Secure Web Communication
TLS connections rely on AES, SHA 2, and elliptic curve key exchange.
Encrypted Storage
Disk encryption systems use AES to protect sensitive files.
Digital Identity and Authentication
Elliptic curve signatures are common in certificates and secure authentication systems.
These examples show that Suite B principles remain deeply embedded in digital security.
Comparing Suite B With Other Cryptographic Suites
Suite B differed from earlier government specific standards by embracing global cryptographic consensus. Unlike proprietary systems, it encouraged collaboration and compatibility.
Suite B Versus Older Classified Algorithms
Older systems relied on secrecy. Suite B relied on mathematics and public scrutiny.
Suite B Versus Post Quantum Efforts
Post quantum cryptography focuses on resisting quantum attacks, which Suite B did not address directly.
Future Outlook of Encryption Standards
Encryption standards continue to evolve. The legacy of Suite B lies in its philosophy rather than its formal existence.
Move Toward Quantum Resistance
Research into lattice based and hash based cryptography is shaping the next generation of standards.
Continued Use of AES and SHA
AES and SHA 2 remain core components of modern encryption and are expected to remain relevant for years.
Best Practices Inspired by NSA Suite B
Organizations can still learn from Suite B when designing secure systems.
Use Standardized Algorithms
Avoid proprietary or untested cryptographic methods.
Match Security Strength to Data Sensitivity
Not all data requires maximum encryption. Balance performance and protection.
Plan for Future Transitions
Cryptographic agility allows systems to adapt when standards change.
Common Misconceptions About NSA Suite B
Many people misunderstand what Suite B represented.
It Was Not a Backdoor System
Suite B algorithms were publicly vetted and widely analyzed.
It Was Not Obsolete Overnight
Even after retirement, its algorithms remain secure and relevant.
It Was Not Limited to NSA Only
Suite B influenced global commercial and government encryption practices.
Conclusion
I see NSA Suite B encryption as a turning point in modern cryptographic history. It demonstrated that strong security does not require secrecy of algorithms but instead relies on transparency, mathematics, and rigorous review. While the formal Suite B framework has been retired, its influence continues through the widespread use of AES, SHA 2, and elliptic curve cryptography. Understanding Suite B helps readers appreciate how today’s secure communication systems were shaped and why open standards remain essential for digital trust in an increasingly connected world.
FAQs
Q1.What is NSA Suite B encryption?
I often explain it as a published set of cryptographic algorithms approved by the National Security Agency for protecting sensitive and classified information. Instead of secret methods, it relied on open and well studied encryption standards.
Q2. Why was NSA Suite B created?
It was created to replace older fragmented and sometimes classified cryptographic systems. The goal was to ensure strong security, global interoperability, and long term trust through publicly vetted algorithms.
Q3. Which algorithms are included in NSA Suite B?
Suite B included Advanced Encryption Standard for data encryption, Elliptic Curve Cryptography for key exchange and digital signatures, and Secure Hash Algorithms like SHA 256 and SHA 384 for data integrity.
Q4. Is NSA Suite B encryption still secure today?
Yes, the algorithms selected under Suite B remain secure and widely used today. AES, SHA 2, and elliptic curve cryptography are still considered strong when implemented correctly.
Q5. Has NSA Suite B been discontinued?
Formally, yes. NSA transitioned away from Suite B in favor of newer guidance. This change reflected evolving security needs rather than a failure of Suite B algorithms.